Top Kubernetes Security Tools in 2025
Explore the essential Kubernetes security tools that detect misconfigurations, vulnerabilities, and enforce best practices to...

Explore the essential Kubernetes security tools that detect misconfigurations, vulnerabilities, and enforce best practices to...
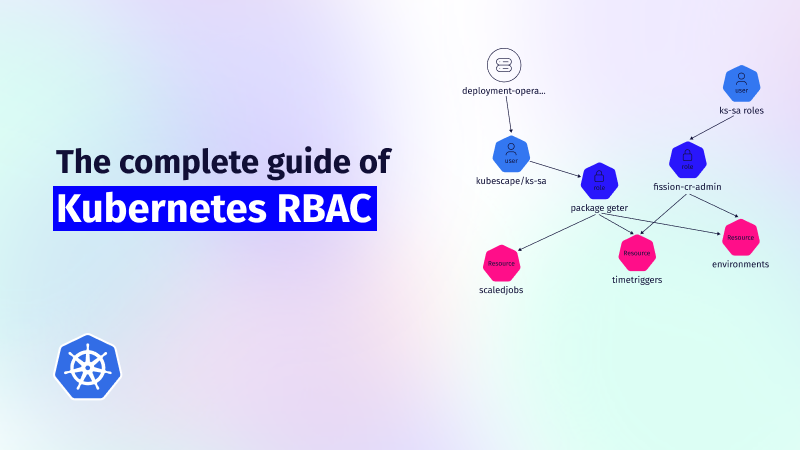
This guide explores the challenges of RBAC implementation, best practices for managing RBAC in Kubernetes,...
Role-Based Access Control (RBAC) is important for managing permissions in Kubernetes environments, ensuring that users...
In 2024, several significant vulnerabilities were identified within the Kubernetes and broader cloud-native ecosystem. In...

Cloud Security Posture Management (CSPM) has become essential for monitoring cloud infrastructure, identifying risks, and...

We’re thrilled to announce a new partnership with OVHcloud, a leading global cloud provider! This...
CIS Benchmarks are a focused set of guidelines for the secure configuration, vulnerability detection, and...
Kubernetes continues to evolve its security posture with version 1.32, introducing several significant improvements in...

We’re honored to share a new partnership with Orange Business (Norway), a global leader in...

Understanding Runtime Security in Multi-Cloud Environments Runtime security in multi-cloud environments encompasses the continuous monitoring...
Originally appeared on The New Stack. More and more organizations rely on Kubernetes to deploy and manage...
The dynamic world of Kubernetes and cloud security is constantly evolving. As we explore this...