ARMO’s new security-boosting summer cocktail: Layered Vulnerability Scanning, SBOM View, and new Auto-Generated Network Policies
This summer ARMO is proud to announce a batch of new features designed to enhance...

This summer ARMO is proud to announce a batch of new features designed to enhance...

ARMO’s new feature revolutionizes Kubernetes vulnerability scanning based on eBPF technology to help Kubernetes and...
In this blog post we will be discussing how we differentiate ARMO Platform from Open...

Introduction In the dynamic landscape of cloud-native cybersecurity, image scanning has become essential to ensuring...

Secure Kubernetes environments without disrupting applications

Struggling to manage vulnerabilities in your Kubernetes environment? You’re not alone. Traditional vulnerability management tools...

We’re thrilled to introduce a fresh ARMO app designed exclusively for Slack, delivering notifications directly...
According to research done by ARMO, 100% of Kubernetes clusters that were tested contained at...
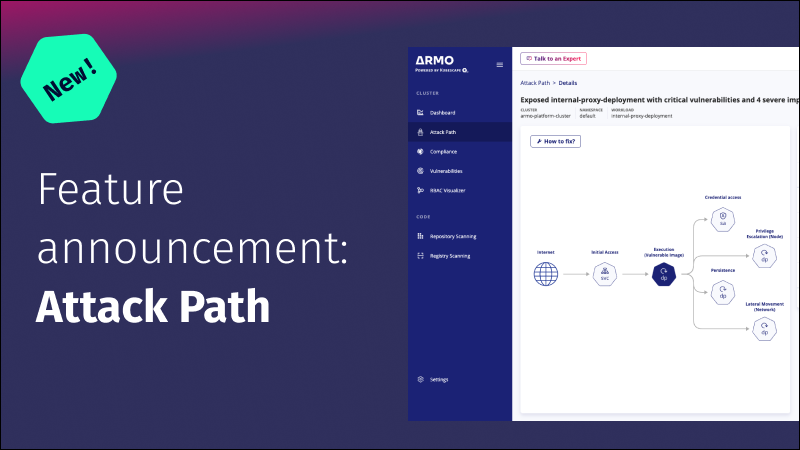
Discover the importance of mapping attack paths in Kubernetes and learn how to effectively enhance...

Enhance Kubernetes security through seamless ARMO Platform and Microsoft Teams integration. Click here to learn...
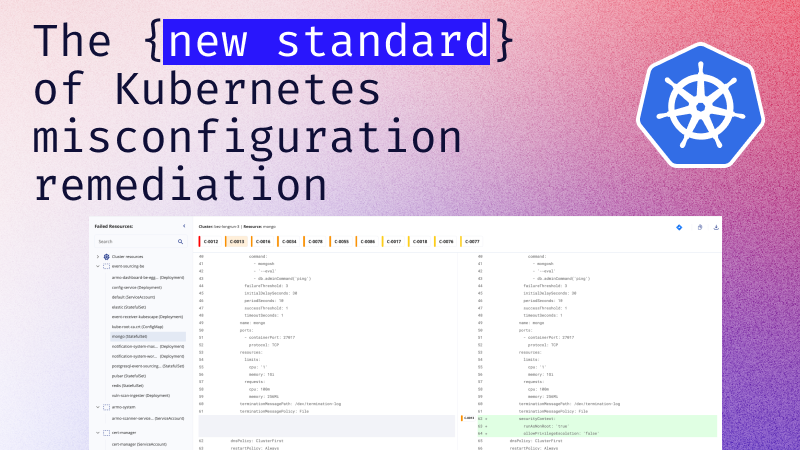
Kubernetes misconfigurations can create security risks and other issues. This article covers common types, their...
RBAC management is crucial to securing a Kubernetes cluster and ensuring compliance with regulations and...